After the NHS cyber-attack, are you doing enough to protect your business?
On May 19th, one in five NHS trusts were victims of the global ‘WannaCry’ cyber-attack, freezing computers used to share patients’ test results and forcing the cancellation of operations scheduled for Monday at a number of major hospitals. The National Cyber Security Centre soon after warned that more cases were likely to be reported at the beginning of the working week as staff switched on their computers. The predicted ‘second spike’, as cyber-security specialists called it, failed to materialise, but a number of hospital trusts are still trying to deal with Friday’s disruption.
Once the dust had settled, so to speak, fingers began to be pointed. ‘Who is to blame?’, asked Alex Hern of The Guardian yesterday morning. ‘In the UK, must the NHS share some of the blame for allowing itself to be so vulnerable?’ It’s a question that is always worth asking, though the NHS, despite its significance, is hardly unique in its vulnerability. During the same attack, several businesses, including the car companies Nissan and Renault and the O2 owner Telefonica were also hit. The Cyber Security Breaches Survey for 2017 revealed soon after that nearly seven in 10 large businesses and just under half of all small businesses had identified a breach or attack in the past year. The largest companies were pressed to pay, on average, £19,600 during the period for reasons relating to those attacks. And then, anyone who’s seen Alex Gibney’s excellent Zero Days and heard the testimony of the pair of Symantec employees who identified the Stuxnet computer virus will know that hacking is no longer––if it ever was––the preserve of the basement-dweller, and is now used for everything from trying to bring about social justice to covert warfare.
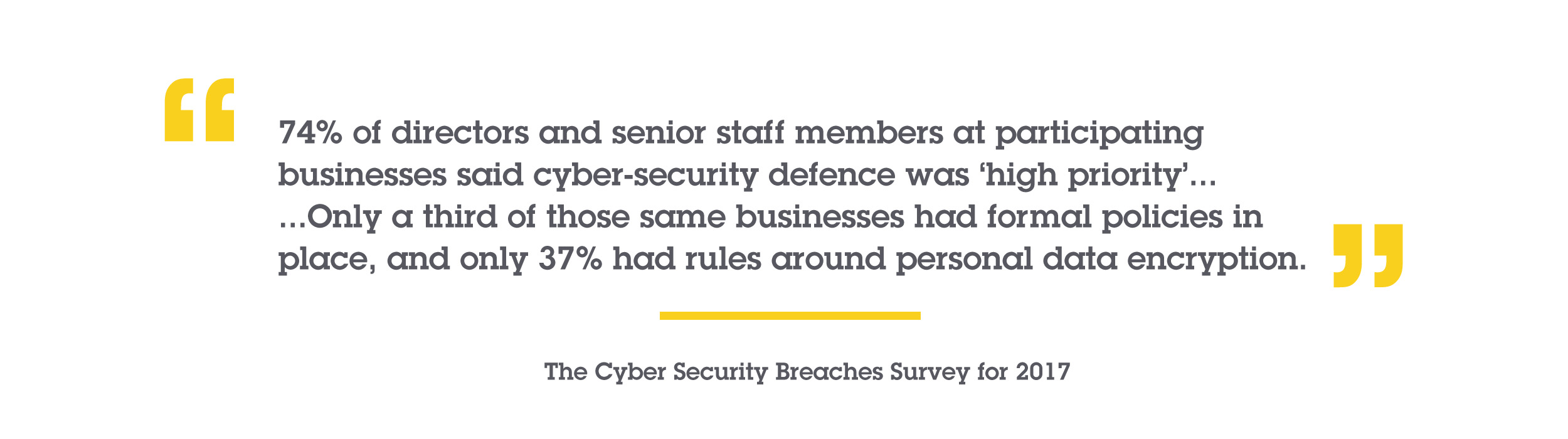
 That isn’t to say that there’s nothing you can do. The Cyber Security Breaches Survey for 2017 also found that though 74% of directors and senior staff members at participating businesses said cyber-security defence was ‘high priority’, it, well, wasn’t. Only a third of those same businesses had formal policies in place, and only 37% had rules around personal data encryption. Just one in five, meanwhile, had their staff receive cyber-security training or attend cyber-security workshops. In 2015, businesses were warned that failing to update their operating systems and patch their computers could have serious consequences. The NHS, as it happens, increased their IT budget in 2015 substantially: Jeremy Hunt told reporters May 19th that a cool £50 million was spent on a new cyber-security ‘centre’ to prevent events like these. Needless to say that in the case of the NHS and for many businesses––those that took the advice, at any rate––the changes made in 2015 still haven’t protected them. And for those who didn’t follow the advice, the consequences have been more serious. Cyber-security is not something done once no matter how comprehensively. Things move quickly in the Digital Age and the measures taken in 2015 may no longer provide adequate protection in 2017. For other businesses the changes they’ve made to protect themselves have been reactive at every step, which is to say that they have always been––and if they don’t rethink their policy, will always be––behind.
That isn’t to say that there’s nothing you can do. The Cyber Security Breaches Survey for 2017 also found that though 74% of directors and senior staff members at participating businesses said cyber-security defence was ‘high priority’, it, well, wasn’t. Only a third of those same businesses had formal policies in place, and only 37% had rules around personal data encryption. Just one in five, meanwhile, had their staff receive cyber-security training or attend cyber-security workshops. In 2015, businesses were warned that failing to update their operating systems and patch their computers could have serious consequences. The NHS, as it happens, increased their IT budget in 2015 substantially: Jeremy Hunt told reporters May 19th that a cool £50 million was spent on a new cyber-security ‘centre’ to prevent events like these. Needless to say that in the case of the NHS and for many businesses––those that took the advice, at any rate––the changes made in 2015 still haven’t protected them. And for those who didn’t follow the advice, the consequences have been more serious. Cyber-security is not something done once no matter how comprehensively. Things move quickly in the Digital Age and the measures taken in 2015 may no longer provide adequate protection in 2017. For other businesses the changes they’ve made to protect themselves have been reactive at every step, which is to say that they have always been––and if they don’t rethink their policy, will always be––behind.
 In 2015, our strategic director Nick Pearce was one of those warning of the threats (in addition to the opportunities) of the so-called Internet of Things and detailed a four-point strategy to aid businesses in defending themselves ‘against a threat you can’t anticipate’. He makes the important point that without eliminating or minimising the threats, your business won’t be in a position to exploit and benefit from the opportunities, and suggests that rather than treat cyber-security as a tedious (if necessary) task to be got out of the way, so to speak, you should see it as a chance to establish your business and yourself as a thought leader, a policy maker and a champion of comprehensive internet defence.
In 2015, our strategic director Nick Pearce was one of those warning of the threats (in addition to the opportunities) of the so-called Internet of Things and detailed a four-point strategy to aid businesses in defending themselves ‘against a threat you can’t anticipate’. He makes the important point that without eliminating or minimising the threats, your business won’t be in a position to exploit and benefit from the opportunities, and suggests that rather than treat cyber-security as a tedious (if necessary) task to be got out of the way, so to speak, you should see it as a chance to establish your business and yourself as a thought leader, a policy maker and a champion of comprehensive internet defence.
As Nick puts it, ‘Lead the battle … a great new world of opportunity awaits’.